Fortifying Venture Capital Due Diligence
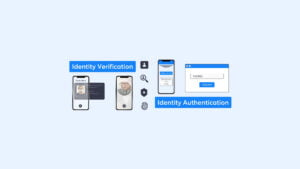
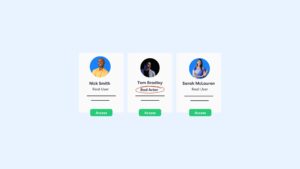
VCs invest capital in high-risk investments, with venture capital due diligence processes being essential. The need for founder and investor due diligence checks requires venture capital compliance solutions with AML and KYC checks.
...